The emergence of cryptocurrency: Explore the world of cryptography, sequel models and 2fa with tap
In recent years, cryptocurrency has gained great grip around the world, attracting millions of users who want to invest in a digital area. However, browsing in this huge market can discourage, especially for those who are new in cryptocurrencies. In this article, we will deepen three essential aspects: cryptography, sequel models and 2fa (authentication of two -factor), a special approach to how they cross the tap stage.
What is cryptocurrency?
Cryptocurrencies are digital or virtual currencies that use cryptography for security and decentralized control. Unlike traditional trustee currencies, cryptocurrencies operate regardless of banks and central governments. The most well -known cryptocurrency is Bitcoin, which in 2009 Created by an individual or anonymous group used by the pseudonym of Satoshi Nakamoto.
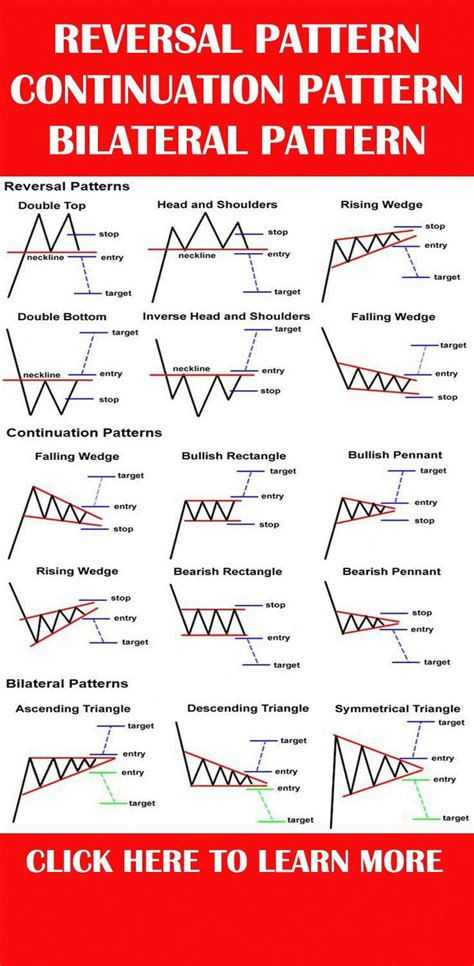
Continuing models
A continuous model is a mathematical concept used to analyze data and set trends. In the context of cryptocurrency markets, it indicates a phenomenon in which cryptocurrency prices tend to follow a specific model before experiencing a significant increase in value. This model usually refers to a period of consolidation (lateral trend) followed by a phase of acceleration, which is characterized by rapid price increases.
2fa: Unrecognized hero
Authentication of two factors (2fa) is a security process that uses two different authentication factors such as someone who knows (for example, its password or pin) and what it has (such as a physical device such as a token or access key or Access Key Biometric Scan). By combining these two factors, 2FA provides an additional safety layer, making it difficult for attackers accessing the accounts.
Tap: hook that attracts users
Bakel is an online platform to reward consumers with cryptocurrencies to perform specific tasks. Peace offers a permanent reward flow, which can vary from a few hundred dollars to thousands of dollars a day. These awards are usually offered to users who are involved in a particular activity or contribute to the community.
intersection: cryptography, sequel models and 2fa
At first glance, cryptography, sequel and 2FA models may look unrelated. However, after a closer inspection, it is clear that these three concepts are very connected.
Cryptocurrencies often experience a significant change in price before accelerating value. This acceleration is a classic example of a continuing model of action. When prices reach a certain level, the market is increasingly confident that the trend will continue, leading to a higher increase in prices.
2FA provides an additional protection layer for users who interact with cryptocurrency platforms such as they will become. When two different authentication factors are required, 2FA complicates the attackers to access accounts and damage the user’s funds. In a sense, 2fa acts as a “security network” that prevents malicious actors from using the system’s vulnerability.
Tap the users involved in these platforms essentially involved in the task series, which together contributes to the growth of the cryptocurrency market. To solve simple mathematical problems or to perform other mini tasks, touch users cryptocurrency awards. These awards encourage consumers to continue communicating with the platform, creating a positive feedback cycle, which increases the total value of cryptocurrency.
Conclusion
Cryptocurrencies have caused a revolution of how we think of digital assets and financial operations. By understanding the intersection of cryptocurrencies, sequel models and 2FA, users can deepen the complex ecosystem that surrounds these markets.